Seen at Ford’s photo shoot for the 50th Anniversary Mustang.
It belongs to HighEye.ca
It is not a virus, it’s a bug in OpenSSL. It is potentially the largest vulnerability in the history of the internet, affecting an estimated two-thirds of secure websites worldwide.
Heartbleed is:
The Heartbleed bug allows anyone on the Internet to read the memory of the systems protected by the vulnerable versions of the OpenSSL software. This compromises the secret keys used to identify the service providers and to encrypt the traffic, the names and passwords of the users and the actual content. This allows attackers to eavesdrop on communications, steal data directly from the services and users and to impersonate services and users.
As security expert Bruce Schneier says “‘catastrophic’ is the right word. On the scale of 1 to 10, this is an 11.”
Very basically – an attacker can move in and out, stealing sensitive data and passwords, and leave zero trace.
Sites that have little lock icon in the URL bar are what’s affected, seen when using HTTPS (like email, Facebook or banking).
Mashable – here / Bruce Schneier – here / Heartbleed site here
Here – Filippo.io
Everyone: change any passwords that may use OpenSSL. Mashable has a list of affected sites here.
Small Business Owners: you need to call your IT guy now. Now. If you are taking credit cards, or any sensitive or private data, you have a responsibility to protect your customers who have trusted you.
Judging eyes :|
This Shangri-lala land we’re living in will soon end, maybe with a massive, worldwide compromise, that will force us to change the way the way we conduct ourselves online. One day, you’ll tell your grandchildren, of a time when people’s passwords were all the same…
This Heartbleed bug is the beginning of that. Go change your passwords.
</rant>
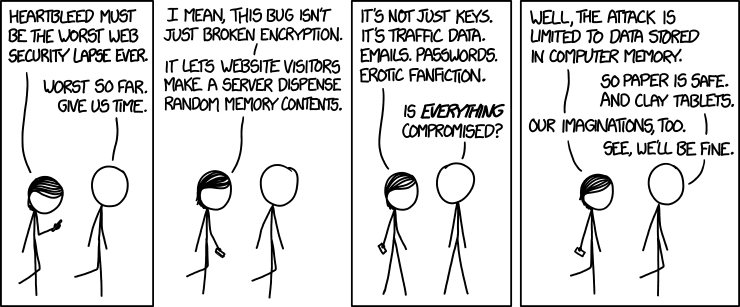
(via XKCD.com)
Imagination.
For years from airports, I’ve tweeted as much:
During a recent trip, I had to send a file out, so was forced to connect.
This is what happened in Chicago O’Hare (ORD):
1 – Boingo is a recognized hotspot provider, okay, I’ll connect to that.
Nope, it’s not working. Oh no, this file needs to go… I have to connect to…
2 – _Free_ORD_Wi-fi Based on the shady name of this network, I bet I’m about to be MITM’d
3 – Yes I was
***
The WiFi network I connected to is likely not affiliated or provided by the airport. Instead, it’s probably an antennae poking out of someone’s backpack.
Using a clever WiFi name, the attacker poses as a legitimate network > I connect to it > now all my traffic is run through the attacker’s computer first, before going out to the internet >as it goes by, the attacker grabs passwords, reads stuff, etc.
(I’ll better explain a MITM attack in the near future)
Don’t go online at the airport. It’s one of the most hostile network in the world. This environment provides nefarious characters anonymous access to sharpen their skills.
If you must go online, avoid entering passwords, accessing sensitive data, and certainly no online banking.
Okay? Okay.
NOTE – this could be because I was already connected to Google+ , then I automatically attempted to reconnect and I was associated to the captive portal yet, although I was getting a suspicious certificate error, it’s because I was being redirected to the captive portal for login first, and that new IP didn’t resolve to “plus.google.com” that is my browser saying woah. Possibly.
Fake LinkedIn invitations are one of the most effective methods of getting a human to click a malicious link.
This type of attack, a phishing attack (or a more targeted, spear phishing attack) works because who doesn’t want to increase their LinkedIn number up to that magical 500+. Plus, LinkedIn is maybe the most reputable of all the social media networks, so that reputation is exploited.
Additionally, LinkedIn is a business-oriented social media site, therefore, most use occurs on a computer attached to a corporate network. And that’s more valuable to a thief than a lone, personal computer.
You receive an email, “Let’s connect!”
It looks like a real, and safe, LinkedIn invitation.
Click on “View Profile” > goes to a fake site > where a virus / malware / etc is waiting > that’s then installed onto your computer > now the attacker has a way into your machine > and potentially the corporate network it’s attached to.
I rely on 2 things – my gut, and LinkedIn’s security (note this method is not 100% fail-safe.)
1 – hmm, I have never heard of this human, and something about the name / company makes my gut say wait….
2 – I open a new browser, go to LinkedIn > Invitations > is the same name on my list there?
If yes: click around to verify identity, check for connections in common, and lots of Googling.
If no: delete the email
***
Don’t be shy to ask for more clarification, proof of identity, reply with “do I know you, and how?”
And always listen to your gut, the best defence against social engineering
Summarized below is what happened, and what to do. But!
Legitimate WordPress sites were used in a DDoS (distributed denial-of-service) attack against other legitimate WordPress sites. The goal is to create a botnet: harness the power of thousands of blogs, and use it to attack another site and take offline, I don’t know the why.
Sucuri is a malware monitoring and cleanup company. They discovered the attack, when one of their client’s went offline due to a DDoS.
From their site:
The attack uses XML-RPC.
XML-RPC is found in the core of WordPress, and is used to perform a “ping”: when one website notifies another website to say hey, there’s new content to see here.
XML-RPC is used to keep search engines updated, RSS feeds fresh, and news sites current. It’s used to create pingbacks and trackbacks, XML-RPC even helps provide mobile access.
XML-RPC is located in WordPress’ core code, and is by default set to ON.
WordPress is in a tough spot with this one.
It makes sense to set the default to ON, right? Pinging is kinda the nature of the internet. There’s lots of plugins designed specifically to take advantage of pinging. That’s why you won’t see WordPress issue a patch for this security breach, they kind’ve can’t.
And that’s why this attack is so clever. Dirty, but clever.
In fact, by turning it off, many core plugins will stop working, as will Jetpack…
It’s up to you, and how you run your site, whether to leave it on or off…
There are 2 ways:
1. search your logs for “any POST requests to the XML-RPC file. If you see a ping back to a random URL, your site is being misused”. – Sucuri
2. use the scanner Sucuri built, click here.
Your URL will be checked against their logs, to verify if it was 1 of the 162,000 affected sites.
This is where it gets tricky, and why I say to read Sucuri’s full post, and comments, and decide for yourself.
Options include:
1. disable all XML-RPC functionality on your site (core plugins may stop working)
2. add the below code to your theme, it’s a preventative filter:
(click here to copy the actual code)
(I chose option 2)
To add this code, is to go deep into the core code of the website (to “hack core WordPress”), where it’s really easy to type one wrong character and break your entire site.
Happened to KeriBlog.
(this stuff, wow eh. I knew what happened, that it was going to be fixed in a minute, and still I coughed up my heart when I refreshed to find that.)