There’s a CRA (Canada Revenue Agency) scam going around right now. I received a call from “Roger” at the CRA this week, asking me verify my current address.
Let’s analyze at the attack.
The Attack
Flag #1
Roger’s number displayed on my phone – 905-XXX-XXXX. Nope.
The CRA agent’s number will never display, it will come up as “Private” or “Blocked” because imagine? People would lose their minds dialling directly to harass the agent.
Flag #2
Roger lists my last 3 home addresses, my company name, then asks for only one piece of information to verify my identity – my birthday. One piece of publicly available information to verify me? No way.
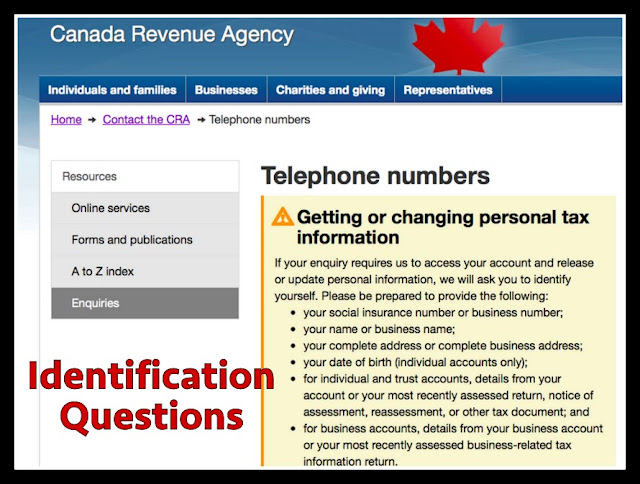
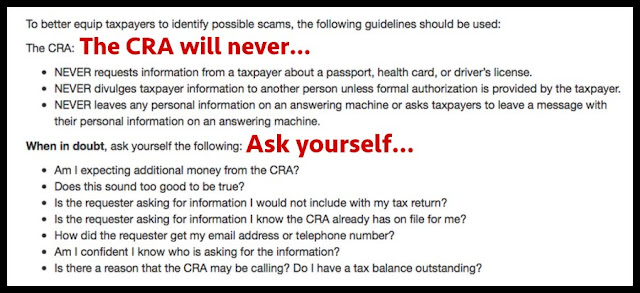
From the CRA website, here’s the list of identification questions they’ll use.
Flag #3
Me: this number on my screen, if I call it back it’ll go to you?
Roger: yes, that will go directly to my desk.
Uh-huh. See Flag #1. Plus, if he’s at his desk, why don’t I hear office noises in the background?
Let’s keep talking.
Me: what’s the problem?
Roger: the address we have on file for your company is incorrect, because the mail we sent you was returned. We need to update your address.
Flag #4
Not only do I have my mail forwarded from my old downtown address, but my accountant and I are very on top of things, so there is no chance this is correct.
I tell him to switch it to my home address, which he has already listed, and he rushes off the phone.
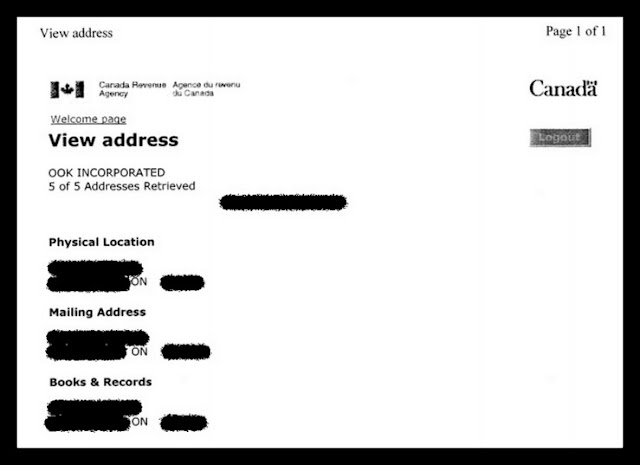
I immediately email my accountant, who searches the CRA database and comes back with this confirmation – my correct address is on file.
Flag #5
I call the number back and it goes straight to voicemail.
Not only is it full and cannot accept new messages, but the name on the voicemail is not Roger.
Flag #6
I trace the phone number, and land up at a suburban house just outside of Toronto. Not posting a map of that, bet the poor guy has no idea his number has been hijacked.
Flag #7
Over to Google, and there’s news everywhere, including one from CBC a couple weeks ago warning Ontario residents. Read it here.
The Defence
– stay sharp and calm… the above played out over 60 seconds, as in, quickly. And if the call comes in while you are distracted or busy, that’s how you slip up and they win
– when in doubt never ever give out personal information, especially your Social Insurance Number (SIN)
– call the CRA directly to confirm the validity. Say something like, “I’m very busy at the moment, but will call you back by end of the day.” That way you’ve initiated contact, and the problem should be listed on your file
– ask lots and lots of questions, they don’t like that
– the scammer will be skilled on the phone, they’ll sound smooth, almost too-smooth…
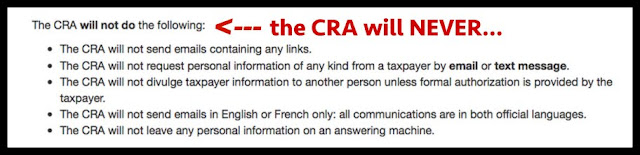
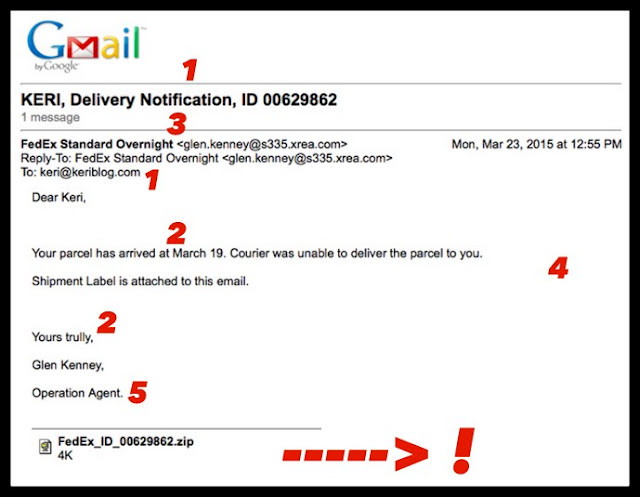
– CRA emails will never contain any links, nor will they contain personal information
– listen to your gut, it’s the best defence in these scenarios
See the CRA website for more details on scams.
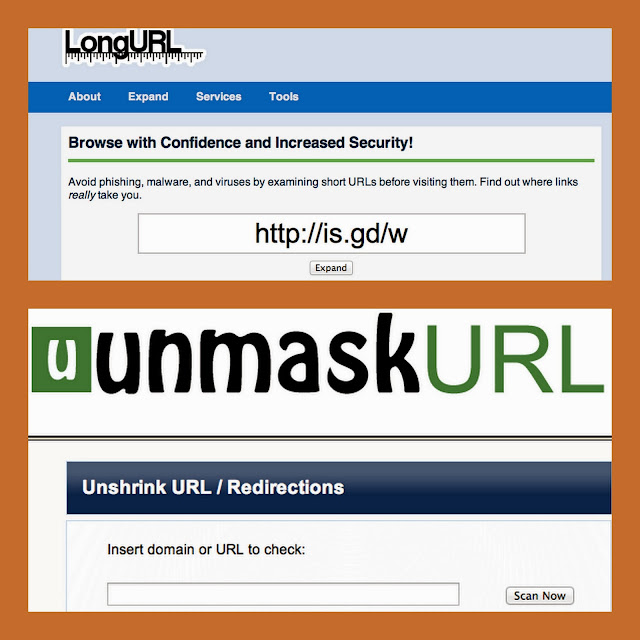
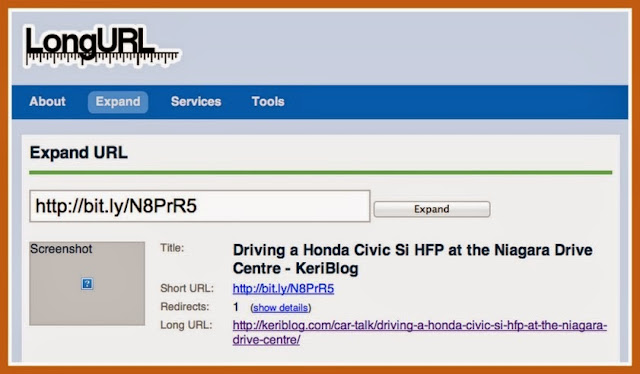
As always in suspicious scenarios, be wary of clicking on links in an email, and if you must, expand the URL before clicking.
Test yourself here – Spot the phishing email
Blog tag = phishing