NFC – Near Field Communication – passing files between two devices, without touching, using radio frequencies.
That Samsung TV ad, where the friends exchange a music file by passing their phones near one-another, but not touching… that’s NFC. Or, how you scan your Visa “tap to pay”…, the Visa machine reads an RFID chip (radio frequency identification)… that’s NFC.
Leave NFC turned OFF to prevent an attack.
Attack example 1: I “bump into you” on the street, you have NFC on, now I have established a connection with your phone, from there it’s dealer’s choice (see also “subway attack“)
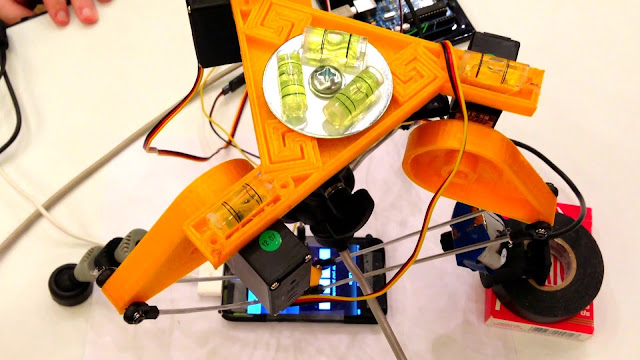
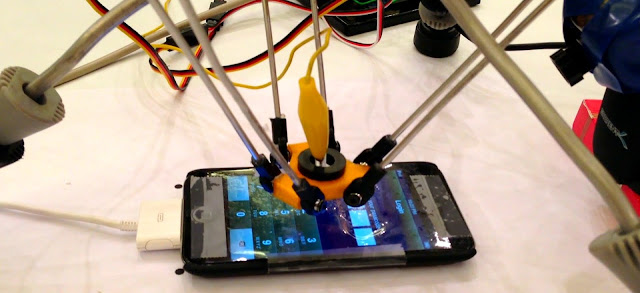
Attack example 2 – an NFC reader is hidden beneath a chair cushion.
The attack:
– target sits on chair
– the credit card in his back pocket is scanned
– attacker now has credit card number & expiry date, and first and last name (that’s what is edited out below)
The defence:
Leave NFC off, and use a RFID shielding sleeve / wallet for your credit cards.