SecTor: Illuminating the Black Art of Security.
Above is the vendor area, and below is the lunch keynote, the talk I was most looking forward to.
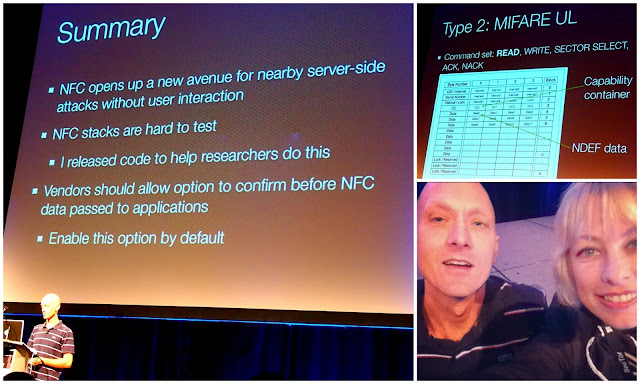
Meet Charlie Miller, one of the world’s best hackers, and, leading expert in a personal favourite topic, NFC.
NFC – Near Field Communication. You likely haven’t heard much about NFC yet, but you will.
Think of those ads on TV, where you put your phone next to your buddy’s, and photo gets beamed over wirelessly. That’s NFC. Charlie has figured out how to use NFC to hack your phone; here he is in action (green shirt).
He brushes close to the victim’s phone, and tada – Charlie can now access and download all the photos, contacts, files, make it call and text… and nothing AT ALL appears on the victim’s phone that would alert him this is happening.
Andorid users: you are, as always, the most susceptible to this attack. Best defense – check ‘yes I want to approve each NFC connection before it happens’.
He also said this, which is so true:
“Real hacking is sitting in your basement watching a phone change every 10 or 20 seconds.” -@0xcharlie at #sectorca
— Steve Werby (@stevewerby) October 2, 2012
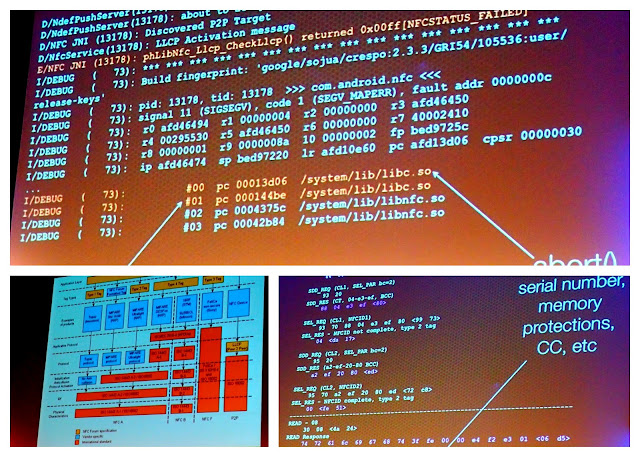
This is what hacking looks like.
And this.
Not all all like that famous Swordfish movie scene, eh.
Above is a contest called, ‘Capture the Flag’; there’s one at most conferences.
I saw a basketball playing robots.
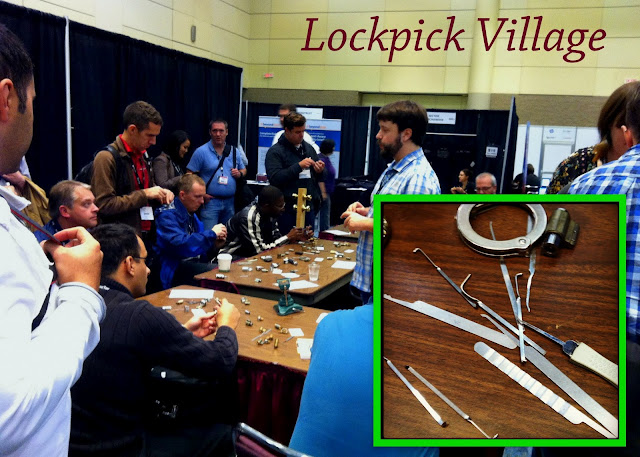
And a lockpick village.
I’ll show you what using those tools looks like on video sometime. Like hacking, it is not at all like in the movies.
Went upstairs for a sunlight break.
SecTor is happening again today, click here for detials.
If you’re intersted in getting into information security, this is your opportunity. It’s a friendly, and resource-rich environment, in an fast-growing industry that has an almost 100% employment rate.
Thanks for a great time, SecTor, and congratulations on your 6th and largest year to date!