Of all the types of malware, this one scares me the most.
Ransomware – a type of malicious software that locks, and sometimes encrypts, the victim’s entire computer. The victim is then informed that removal is only possible, when they pay a ransom fee to the creator of the malware. Basically, ALL your files get locked up, and someone else has the key.
The Attack
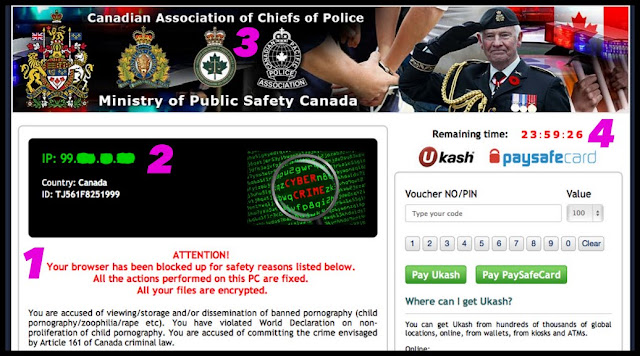
On my other computer, I was catching up on celebrity gossip, and streaming TV from a sketchy Eastern European site, when this page overtook my browser.
1 – informs me all my files have been encrypted
2 – shows my IP address, which didn’t pinpoint my exact physical location, but was pretty close
3 – ransomware often uses this popular ‘police-theme’, to give the illusion of authenticity, and heighten fear
4 – a scary countdown timer; I have 24 hours to pay the ransom
The Defence
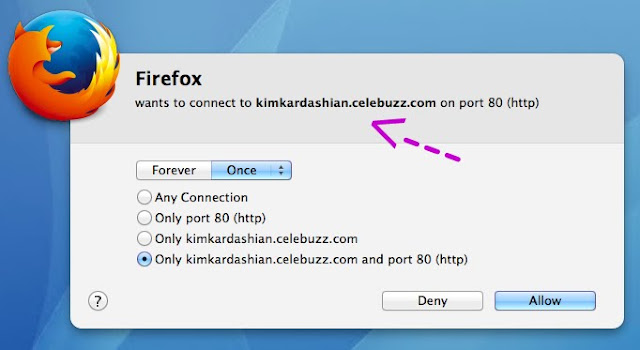
Ransomware is usually installed from clicking a bad link on social media, in a website or email, opening a malicious email attachment, or sometimes just visiting a malicious site.
A closer investigation reveals this is mostly scareware. The English is poor, I’m on a Mac not a PC, the “Internet Police Department” uh-huh, and child p0rn phft as if, I don’t even really like kids.
Plus, 24 hours have passed, and my computer is fine.
Notice though, I said “my other computer“.
Because never would I visit those sites on my work computer. Which is why, had this actually happened, my solution would be to wipe the entire laptop, wouldn’t matter, there’s nothing on it. Opposite of this computer.
Keep your anti-virus software updated, your firewall on, and be careful what you click.
The Fix
It’s up to you if you decide to pay the ransom.
F-Secure has removal instructions, as does Norton. Or take you computer to your trusted IT repair place.
Regularly backup your files.