That’s scary that Healthcare is only 43%, now that many medical machines and devices are internet-enabled. I was surprised Technology was just 50%, and last place’s 27% will surprise no one.
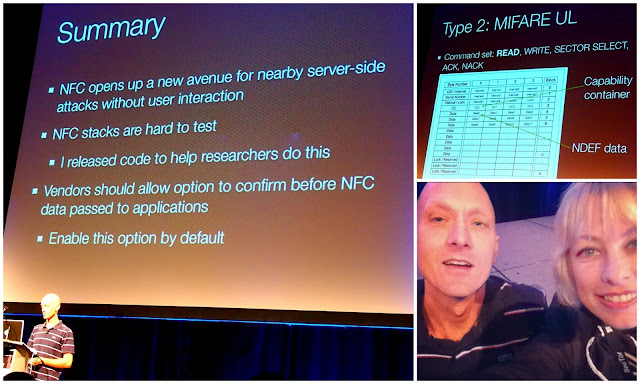
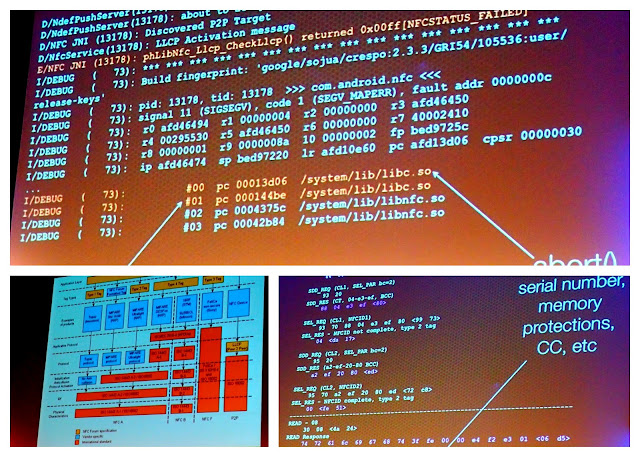
Speaking is Chris Wysopal, co-founder and CTO of Veracode – a premiere application security company. As in, good source.
From SecTor 2015.